I realize that my earlier post was a bit short. There are those days that I try to put out a tutorial (based on my daily goal) and end up not having a lot of time. I apologize for the short post, but I’ve got the rest of the details.
After you’ve installed Firestarter you’ll need to initially run it and configure it. Since Firestarter is a security application it will need to be run as an administrator. After installation run the following:
ALT-F2: gksudo firestarter
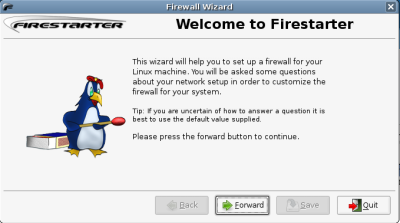
You will be prompted for your admin password and then firestarter will begin the initial Firewall Wizard. As this wizard mentions, if you are unsure about any of the settings it is generally safe to assume the defaults.
Step 1: Welcome to Firestarter
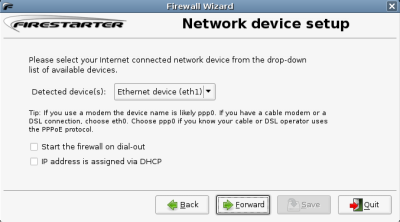
Step 2: Select your network device.
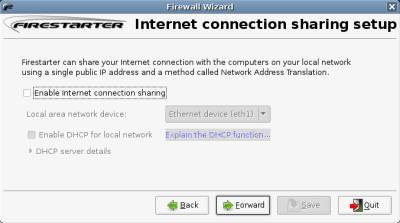
Step 3: Do you need to share this device with another machine?
Step 4: You’re ready to start creating rules.
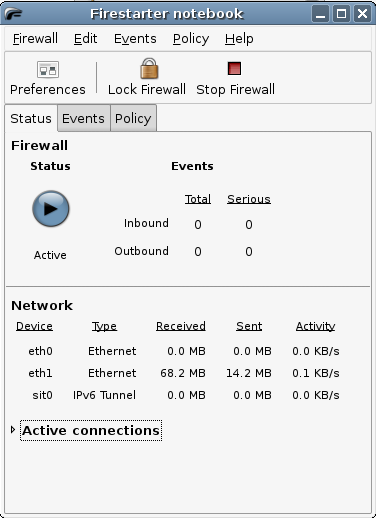
As you can see from this last screenshot the interface is fairly simple. You can see the current status (Active) which can be turned off using the “Stop Firewall” button to the top.
You may need to turn on / off the firewall as you create rules. In some cases your firewall will block needed traffic. In this case you can troubleshoot things by turning off the firewall while you get used to creating rules.
If there have been any events (firewall notifications) you can see those listed in the events tab. This is where you can see if anyone is trying to access your machine, where they are coming from and what port they are trying to connect to. As you watch this you’ll be able to create custom policies.
To create a policy simply select the policy and create in incoming or outgoing network policy. A simple explanation of these are:
incoming: what do you want to allow in to your machine.
outgoing: where do you want to be able to go out of your machine. outgoing policies can be used to filter traffic or websites (ie; parental filters, blocking microsoft.com, etc) ;)
outgoing policies can be set using whitelisting or blacklisting policies. of course, whitelisting is permissive by default and blacklist is restrictive. Try a few things and test out your firewall. Firestarter is very easy to use. It generally takes a minute or two to know where to create your rules, but after that you can lock down your machine to your comfort.
Update: per the comment left by Chris below it should be noted that whitelisting is more restrictive than blacklisting as it only allows the sites included in the whitelist. Blacklisting specifically denies only the sites listed in the blacklist.
Technorati Tags: firestarter, firewall, gnome, ubuntu, usage
Pingback: meneame.net
You mention that white-listing is permissive by default and black-listing is restrictive. Although true, this is potentially confusing for users. White-listing restricts all sites that are NOT listed. Black-listing restricts all sites that ARE listed.
As such, using white-listing is MORE restrictive than black-listing.
Pingback: » Setup a Desktop Firewall with Firestarter : Ubuntu (5.10 / 6.06.1 / 6.10) Ubuntu Tutorials : Breezy - Dapper - Edgy - Feisty
How to setup Firestarter to start up every time the computer starts?
Raj – firestarter will load automagically when you boot but the GUI will not. The services and firewall are running I guess is another way to say it.
If you need to access the GUI to make changes you’d need to launch it but by default it isn’t loaded.
Pingback: El Módem » Blog Archive » Firestarter, un firewall para Linux
Pingback: furuikeonline blog » Blog Archive » Using Firestarter : Ubuntu (6.10)
Hi I’ve added a screncast http://wikisos.org/wiki/Ubuntu_7.04:How_to_setup_Internet_connection_sharing that shows how to install firestarter and enable Internet connection sharing
Hi I’ve added a screencast http://wikisos.org/wiki/Ubuntu_7.04:How_to_setup_Internet_connection_sharing that shows how to install firestarter and enable Internet connection sharing
I followed the tutorial but users on my system can still browse. Their browser comes up with the following error: The proxy server is refusing connection. What am I doing wrong?
I have firestarter running at home and at work and it’s an excellent tool.
However, I have a question. In the list of traffic under the events tab, some items are coloured red and others are black. What’s the significance of the red ones?
It looks like the attempts on ports on which I have services running are in red but there’s nothing in the help (the links don’t work) to confirm this.
** “some items are coloured red and others are black. What’s the significance of the red ones?”
red=incoming traffic requesting access
black=outgoing traffic requesting access
** Hi Christopher, in your first post you mention:
“the best policy on an unprotected machine is no-incoming policy. It’s always the safest route to be able to get out but not let anything in.”
Could you by post,link, etc please show how exactly to block all incoming traffic?? How to allow or add permission for programs that need incoming traffic and pose no threat to the machine.
Thank you.